- Lacoon Mobile Security
Looking for how to make a USB security key more secure? Creating a USB security key is a simple and effective way to protect your computer from unauthorized access. By creating a bootable USB key, you can ensure that only authorized users can access your system. Check out this tutorial to learn how!
What is a USB Security Key?

The advanced method of login authentication is via the USB Security Key or the physical security keys. This USB key is part of two-factor authentication and can be used to lock and unlock the computer. Hackers would have a difficult time obtaining the key.
This type of physical security key can be obtained from manufacturers such as Google, Yubikey, or Thetis. They are, however, expensive.
You can create your own USB login code for a cheaper alternative. You will need to either compromise your USB drives or purchase a Pendrive that is specifically designed for this purpose.
Security Beyond the Password

The Universal Serial Bus security keys will increase security by a new level. This physical security key eliminates a number of problems.
A key logger can look stupid if there is no password. Brute force attacks can be very slow because even if the attacker cracks the password, they still need a physical key. However, a password manager will allow you to forget those complex passwords and keep them in check. That would be great!
Don’t be too excited. There are also some downsides. First, not all websites accept a physical U2F token for authentication. If your key is lost or damaged, you may still be unable to access your accounts and devices.
Let’s not lose sight of the goal. Let us show you how to create your own USB security keys for unmatched security.
USB Unlock keys: The Good and the Bad
Relying solely on passwords is a huge security mistake that can lead to problems down the line. Even if you create strong passwords and have good security habits, there is one problem: a password, once it has been discovered, it is no longer secure.
A physical key is easier to compromise, and tangible keys are more difficult to steal than intangible thoughts.
Another benefit is the elimination of password memory. However, this issue is much less if you use a secure password manager. Depending on which software is used to create the USB key, there are additional benefits.
It’s not all roses and sunshine.
One, it’s likely that you will have headaches if the USB key is lost or damaged. Key recovery can be more difficult than setting a password. The key also permanently occupies Universal Serial Bus port space. If you want to give someone access to your key, you will need to physically hand it to them.
Before you decide to set up a USB security code, you will need to evaluate the pros and cons.
How To Turn A USB Into A Security Key On Windows PC

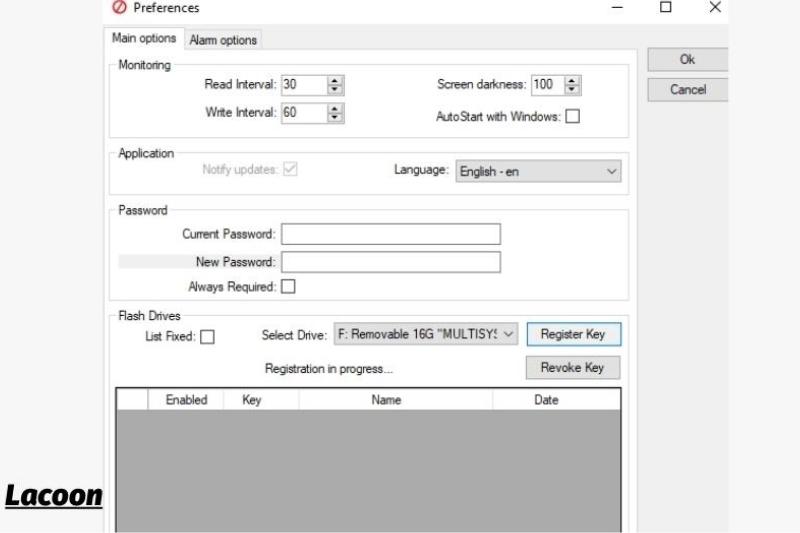
There are many options available to you if you’re looking for ways to secure your Windows 10 computer. We will show you how to use a USB Raptor. It’s free, and you can also get support from the paid app if needed. Rohos LogonKey, one of the paid apps, works on both Windows and Mac.
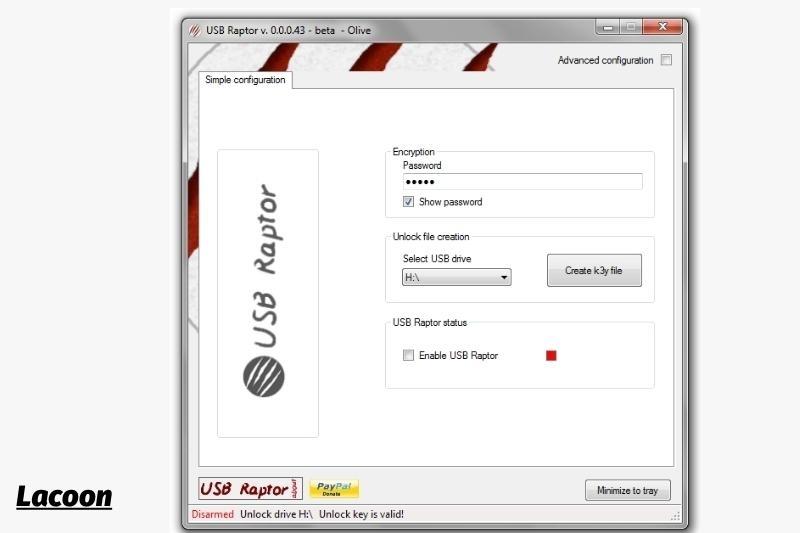
Here is how to make a USB security code using USB Raptor
- Navigate to the USB Raptor Project on SourceForge, and click Download.
- The USB Raptor software can be saved to your computer.
- Extract the Universal Serial Bus Raptor archive and place it at the desired location. Then, run the USB Raptor application.
- Please read the Terms of Service and indicate that you have. Click I Agree to Proceed.
- Enter a password in the encryption field.
- Click Create key File to select the Universal Serial Bus drive that you’ll use for your key.
- Check the box next to Enable USB Raptor.
- In the upper right corner, click the Advanced configuration checkbox.
- Click the checkboxes next to the following in the General Settings tab
- Start USB Raptor in Windows Startup
- Start in the system tray
- USB Raptor is always armed (To disable Universal Serial Bus Raptor, click the checkbox labeled ‘Enable USB Raptor’ to uncheck it.)
- To minimize, click on tray
- USB Raptor will start the next time your computer turns on. The computer will lock if the USB key isn’t in place.
How to Make a USB Key for Your Mac

Although there isn’t a free Universal Serial Bus security app for macOS, there are many options that offer a free trial. Rohos Logon Key can be used on both Windows and Mac. It offers a free trial, so it’s worth checking out whether you are using only Macs or a combination of Macs.
Rohos Logon Key is an extra layer of protection that’s not available with a USB Raptor for Windows. It is impossible to log in if you don’t have the key installed. Rohos Logon Key Mac makes it a little more secure.
This is how you can create a USB security code for Mac with a Rohos Logon key:
- Navigate to the Rohos Logon Key for the Mac website and click Download.
- Navigate to the Downloads folder or wherever your downloads are saved and then unzip the files. Click on the RohosLogon installation.
- Continue
- Click Continue > Accept.
- Click Continue after selecting Install for all users.
- Click on Install.
- If prompted, enter your username and password and click Install Software.
- Click Close
- Connect a USB flash drive to your Mac.
- Open Rohos Logon Key, and click USB Drive.
- Click OK to select the USB drive that you wish to use.
- From the dropdown menu, select Lock the desktop.
- Rohos Logon Key protects your Mac now that the Universal Serial Bus drive has been disconnected.
Three Tools to Make a USB Flash Drive a USB Security Key

These three tools will help you create a Universal Serial Bus security code if you have enough flash drives. These tools are easy to use and will help you create a USB security code.
1. Predator
A predator is a popular tool for turning a USB drive into an access control device.
Predator was free to Home users once. The situation has changed. A Home Edition license costs $10. It costs $15 per computer for commercial and professional environments. There is no support. Predator Professional includes one-year support and costs $30 per computer.
Access to the computer can be granted as long as the USB drive remains plugged in. The keys used for USB drives will not be altered. Files will not be deleted or altered in any way.
Advanced features include:
- Multiple computers can be locked/unlocked with one Universal Serial Bus drive.
- Multiple USB drives can be assigned for different users.
- A built-in scheduler allows you to limit your computer access to specific times of the day.
- Schedules can also be set up per user.
- Per-user passwords may be used in lieu of a USB key that is lost or damaged.
- Regular updates to the USB drive security codes limit the effectiveness of copied USB drives.
Predator is an excellent choice if you need a simple and quick solution to your Universal Serial Bus security problem. This program is among the most flexible and powerful on this list.
2. Rohos Logon Key Free
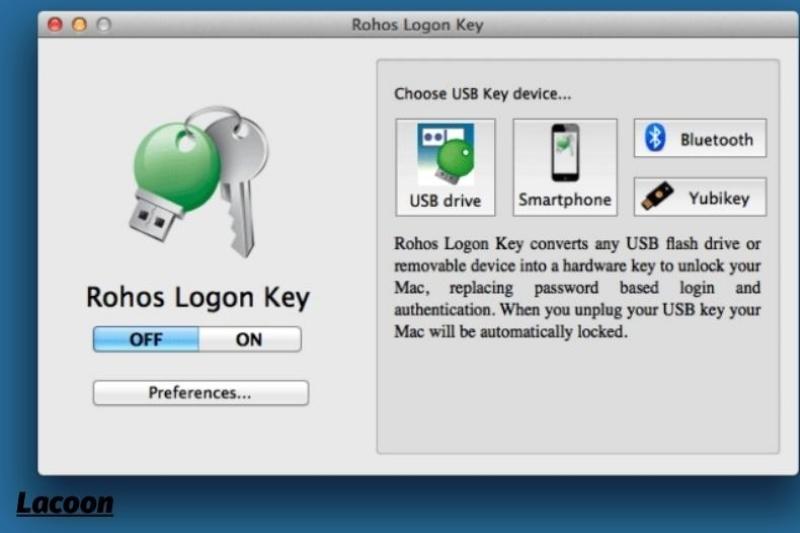
Rohos Logon Key Free, a multi-platform access control software that can create USB keys on Windows or Mac, is available.
Although there is an unlimited version that includes many key features that are missing (no pun intended), it’s only for Windows. You will need to pay $35 if you want complete security and protection or if your Mac is used.
Rohos stores your login information and then automatically enters your credentials when the Universal Serial Bus plug is in. Alternative logon options exist for Android or iOS. This allows you to access your Windows or Mac computer via your smartphone.
These features include:
- Two-factor authentication with a USB key or PIN code is possible.
- You can access the emergency logon system in the event of a broken or lost Universal Serial Bus, or for any forgotten PIN code.
- USB key devices protect passwords against unauthorized duplications by encrypting them with AES256.
Predator is more difficult to set up than Rohos. Rohos, however, is simpler and fundamentally different. You can use it as a replacement for entering credentials. Simply plug it into the unlock screen to unlock.
This, of course, makes it less secure than Predator, so you should only use Rohos if you specifically need the USB-as-login-credential functionality rather than Predator’s keep-plugged-for-access functionality.
You should also note that two-factor authentication is not available for free accounts. This is an important security feature and should be considered when selecting your Universal Serial Bus security keys.
3. USB Raptor
USB Raptor, a free USB security app that you can use for locking your Windows computer, is available as a download. Raptor locks your computer when the USB flash drive is removed from the system, just like other USB security options.
USB Raptor functions as a portable application. To use it on your computer, you don’t have to install it. Just run the executable and configure your USB drive.
These features include:
- Pair unlock file with serial number for USB flash drive
- Lock drive screen customization
- Always lock the system
- USB Raptor’s interface is simple to use. It is easy to use USB Raptor.
What about Hardware Security Keys
There are also off-the-shelf USB Security Key options available if you don’t want third-party Universal Serial Bus keys.
Examples include the very popular Yubico YubiKey, its variants and the Google Titan Key. These are only a few of the many options available, but they represent the best on the market.
You are making a significant step towards increasing your security, no matter what option you choose – a third-party USB key or an off-the-shelf option.
USB Security Keys: Useful and Required

A USB security key plugs into a computer to communicate with it to inform it that an authorized user attempts to access the account(s).
It works with a USB security application that continuously scans your USB ports looking for compatible devices (the key), which will then locate the key and encrypt it. The computer locks if it’s not located until the USB security keys are plugged in.
These devices use the Universal Second Factor (U2F), an open standard managed and maintained by the Fast Identity Online Alliance (FIDO).
Privacy and Security Guaranteed
Two-factor authentication is used to protect against attacks like man-in-the-middle (brute force), man-in-the-middle (phishing), session hijacking and spear phishing). User identities are also checked against unique keys, not personal information.
These identities are used to verify the authenticity of users. Privacy is protected at all times. These digital identities can be linked to government identities for a higher level of authentication.
Quick, easy, and Cheap Solutions
Low-cost (or cheap!) These keys are available as open-source backend architecture from third parties or can be configured by yourself.
Once the key has been created, authentication can be performed instantly using supported browsers and applications such as Opera, Mozilla Firefox, Google Chrome, and Mozilla Firefox.
More:
FAQs

1. Why should I invest in USB security keys?
You don’t need to spend unless you decide to purchase a commercial product. Following the instructions above, you can create your own USB security key.
This is a good idea because two-factor authentication has been shown to be more secure than single-layer password protection for data security. It is essential to take additional security measures in an age of increasing account thefts and data leaks.
Physical USB security keys are the best way to ensure your accounts are secure. They can only be used by you unless you steal them.
2. Isn’t it tedious to create multiple keys for every device?
You don’t have to do this, of course. The USB security keys work just like regular keys. You can attach a padlock to different doors and then open it with the exact same key. This allows you to access all associated accounts from any device or location with the same security key.
You can also configure separate keys if you prefer additional security.
3. How can I locate my security key?
Open the root folder and navigate to misc> Wi-Fi to view the Wi-Fi security code in the wpa_supplicant. Conf file. Alternatively, install an Android terminal emulator and issue the cat /data/misc/Wi-Fi/wpa_supplicant. To view file contents and to see the network security key, use conf
Conclusion
These are several techniques for converting a USB drive into a USB security code. Physical keys are more secure than passwords, and they may be used for a variety of things. At present, these keys can only be used to lock and unlock the device; however, they will soon be able to access your accounts.
Lacoon hopes that you found these tips useful! If so, please share this tutorial with your friends and colleagues